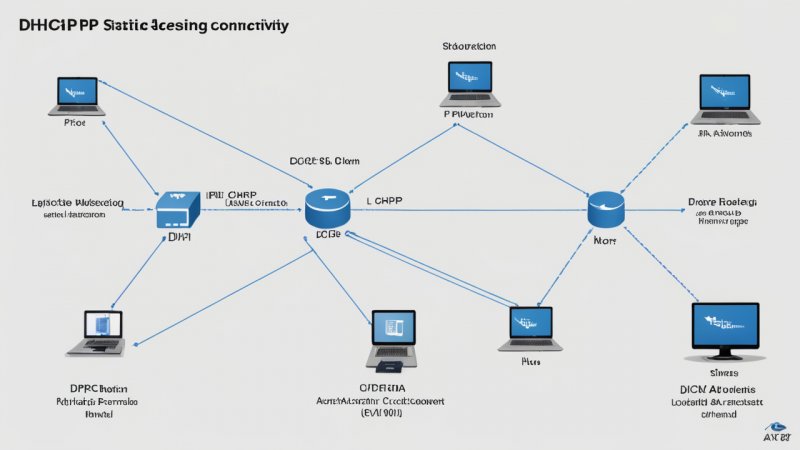
Network Protocols
Dive into the intricate realm of network protocols where we provide extensive information on various types of protocols, their roles in networking, and their significance in ensuring smooth and secure data transmission. Our collection includes detailed explanations, practical implementation examples, and relevant case studies to enhance your understanding of network communication standards and practices.