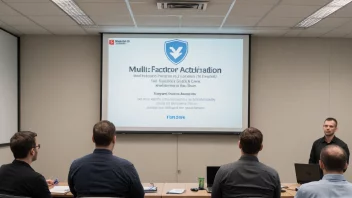
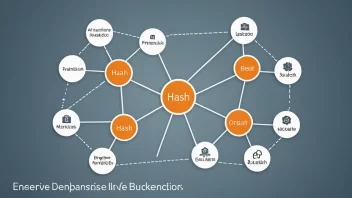
security
This tag explores the security aspects of cryptographic hashing, including its effectiveness in preventing tampering and fraud, common vulnerabilities, and best practices for implementation.

Software Development Practices
The Importance of Security in Software Development: Comparing Reactive vs. Proactive Approaches