In the age of digital information, where data breaches and unauthorized access are prevalent, cryptographic hashing algorithms have emerged as a critical component of cybersecurity. These algorithms serve as the backbone for ensuring data integrity, safeguarding passwords, and enabling secure blockchain transactions. Understanding how these hashing algorithms work, their implementation in various applications, and their significance in maintaining the security of digital systems is essential for anyone involved in technology today. This article delves deep into the world of cryptographic hashing, exploring its principles, applications, and best practices.
The Basics of Cryptographic Hashing
A cryptographic hash function transforms input data of any size into a fixed-size string of characters, typically in hexadecimal format. This output, known as the hash value or digest, represents the original data uniquely. A few key properties define the effectiveness of a cryptographic hash function:
- Deterministic: The same input always produces the same output.
- Quick Computation: It should be fast to compute the hash for any given input.
- Pre-image Resistance: It should be computationally infeasible to reverse the hashing process to retrieve the original input.
- Small Changes Result in Large Changes: A tiny alteration in the input should produce a significantly different hash.
- Collision Resistance: It should be improbable for two different inputs to produce the same hash output.
Applications of Cryptographic Hashing Algorithms
Cryptographic hashing algorithms have a wide range of applications, acting as a fundamental technology in various fields:
Data Integrity
One of the primary uses of cryptographic hashing is to ensure data integrity. By generating a hash value of a file or dataset, users can later verify that the data has not been altered. This is particularly useful for software distribution, where a hash can confirm that the downloaded file matches the original. For instance, many software companies provide a hash (like SHA-256) alongside their downloads, allowing users to verify the integrity of the software.
Password Storage
Storing passwords securely is a significant challenge for developers. Rather than saving passwords in plain text, systems can store the hashed version of passwords. When a user attempts to log in, the system hashes the entered password and compares it against the stored hash. This way, even if the database is compromised, attackers cannot easily retrieve the actual passwords. Common hashing algorithms used for password storage include bcrypt, Argon2, and PBKDF2, which also incorporate salting to further enhance security.
Blockchain Technology
Cryptographic hashing plays a crucial role in blockchain technology, which underpins cryptocurrencies like Bitcoin. Each block in a blockchain contains a hash of the previous block, creating a secure chain of blocks. This structure ensures that any attempt to alter a block would invalidate all subsequent blocks, making tampering extremely difficult. Additionally, the hashing process is integral to the mining process in proof-of-work systems, where miners solve complex mathematical problems to validate transactions and create new blocks.
Digital Signatures
Another important application of cryptographic hashing is in digital signatures. In this context, a hash of a message is created and then encrypted with a private key. The recipient can verify the authenticity of the message by decrypting the signature with the sender's public key and comparing the hash to the message's hash. This ensures both the integrity of the message and the authenticity of the sender.
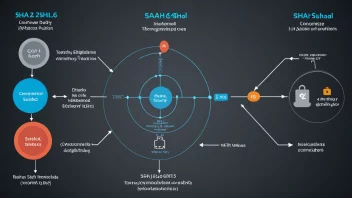
Popular Cryptographic Hash Functions
Several cryptographic hashing algorithms have gained popularity over the years, each with its unique features:
- MD5: Once widely used for checksums, MD5 is now considered insecure for cryptographic purposes due to vulnerabilities that allow collision attacks.
- SHA-1: SHA-1 was a standard for many years, but it has been phased out in favor of more secure options due to similar vulnerabilities.
- SHA-256: Part of the SHA-2 family, SHA-256 is widely used in security applications and protocols, including SSL/TLS and blockchain.
- SHA-3: The latest member of the Secure Hash Algorithm family, SHA-3 offers enhanced security and flexibility.
- Bcrypt: Designed specifically for hashing passwords, bcrypt incorporates a work factor to slow down the hashing process, making brute-force attacks more challenging.
Implementing Cryptographic Hashing
Implementing cryptographic hashing in applications involves selecting the appropriate algorithm and applying best practices. Here are some guidelines:
- Choose the Right Algorithm: Select a hashing algorithm that meets your security requirements. For passwords, prefer algorithms like bcrypt or Argon2.
- Use Salting: Add a unique salt to each password before hashing to prevent rainbow table attacks.
- Update Hashing Mechanisms: Regularly review and update your hashing mechanisms to adopt newer, more secure algorithms as they become available.
- Verify Hashes: Implement processes for verifying hashes, especially for data integrity and password authentication.
Case Studies
Several notable case studies illustrate the importance of cryptographic hashing:
1. The Target Data Breach
In 2013, Target suffered a massive data breach, exposing the personal information of millions of customers. Investigations revealed that weak password storage practices contributed to the breach, highlighting the need for secure hashing algorithms.
2. Bitcoin and Blockchain Security
Bitcoin utilizes SHA-256 for its hashing needs, ensuring the integrity and security of transactions. The blockchain’s structure, dependent on cryptographic hashing, has proven resilient against tampering, establishing trust in decentralized systems.
Conclusion
Cryptographic hashing algorithms are indispensable in the modern digital landscape, providing essential security features that protect data integrity, secure password storage, and enable trust in blockchain technology. As cyber threats evolve, understanding and implementing effective hashing practices becomes increasingly critical for individuals and organizations alike. By selecting appropriate hashing algorithms and adhering to best practices, we can build a more secure digital future, safeguarding sensitive information against unauthorized access and ensuring the integrity of our data.